Anycast is a way of communicating with a network where incoming requests can be sent to various locations or “nodes.” In the case of a CDN, Anycast sets up incoming traffic routes to the nearest data center to process the application efficiently. The selected route allows the Anycast network to be more tolerant in the face of high traffic volume, network congestion, and DDoS attacks.
How does Anycast Work?
An anycast network router can deliver incoming communication requests to multiple data centers. When requests enter a single IP address associated with the Anycast network, the network distributes the data according to another priority. The post-selection process for selecting a specific data center will be designed to minimize delays by choosing a data center and a very short distance for the applicant. Anycast is characterized by 1-to-1 multi-organization and is one of the five main network protocols used in the Internet protocol.
Why Use an Anycast Network?
If multiple requests are made simultaneously on the same Origin server, the server may be frustrated by traffic and may not respond correctly to other incoming requests. With the Anycast network, instead of a single Origin server that carries a large amount of traffic, the load can spread to other available data centers, each of which will have servers capable of processing and responding to incoming requests. This route forwarding may prevent the original server from expanding capacity and avoid service interruptions for customers requesting content from the original server.
What is the Difference between Anycast and Unicast?
Most Internet operators operate a routing scheme called Unicast. Under Unicast, every node in the network receives a different IP address. Home and office networks using Unicast; when a computer is connected to a wireless network and gets a message that an IP address is already in use, there is a conflict of IP address because another computer on the same Unicast network is already using the same IP. In most cases, that is not allowed.
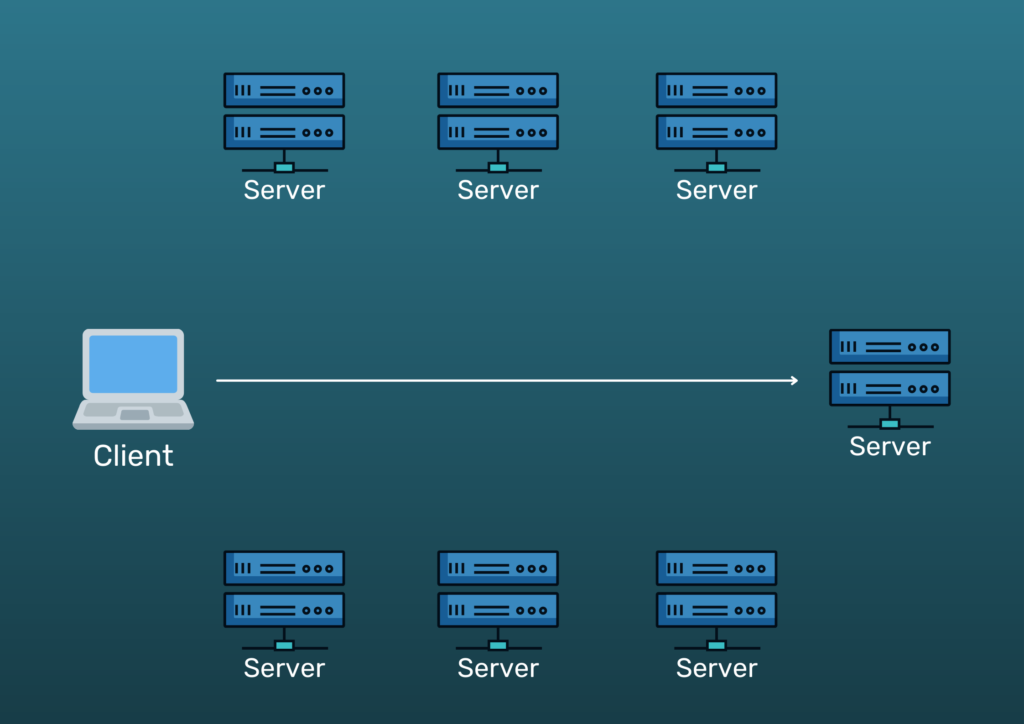
When a CDN uses a unicast address, traffic is transferred directly to a specific location. This poses a risk when the network encounters unfamiliar traffic, such as a DDoS attack. Because traffic is transmitted directly to a particular data center, its surrounding area or infrastructure may be congested with traffic, resulting in the refusal of services in legal applications.
Using Anycast means the network can be highly tolerant. Because traffic will find a better route, the entire data center can be sent offline, and traffic will automatically move to the nearest data center.
How does an Anycast network mitigate a DDoS attack?
After some DDoS mitigation tools filter out some of the attack traffic, Anycast distributes the remaining attack traffic to multiple data centers, preventing any single site from being frustrated by applications. If the capacity of the Anycast network is greater than the attack traffic, the attack is effectively reduced. In many DDoS attacks, many malicious “zombie” or “bot” computers are used to create what is known as a botnet. These machines can be scattered across the web and generate so much traffic that they can destroy a standard Unicast-connected machine.
The appropriate Anycasted CDN expands the available network space so that refractory refusal traffic from distributed botnets will be entered by each CDN data center. As a result, as the network grows in size and capacity, it becomes more and more challenging to introduce active DDoS to anyone using the CDN.
It is not easy to set up an authentic Anycast network. Proper use requires a CDN provider to maintain its network hardware, build direct relationships with its rising carriers and set up its own communication channels to ensure that traffic does not “hit” between multiple locations.