The BlackEnergy malware first appeared in 2007. The malware was designed to launch DDoS attacks, as well as download plug-ins designed for spam, banking cyber-attacks etc. It has been used for the same tasks even in recent years, such as when targeting the State Bar of Georgia last May
Following the latest cyber attack, the office had to suspend normal operations. They started investigating and found that BlackEnergy was used alongside eight suspect domains.—clusteron[.]ru, svdrom[.]cn, funpic[.]org, logartos[.]org, pizdos[.]net, weberror[.]cn, h278666y[.]net, and inattack[.]ru—as indicators of compromise (IoCs).
Previously, these web properties would be used to get a glimpse of the world beneath but now we can dive deep into WHOIS and DNS records. This led us to an alarming discovery!
- The domains identified as IoC resolved to 49 IP addresses
- This email was protected from spam bots by email services such as Google, Yahoo, Hotmail and AOL.
- You might want to assess the business email addresses or IP addresses of 6,003 domains – 141 of which are known to be trying to infect your computer with malware.
Please take a look at the artifacts we obtained from our analysis of your data – you can download a sample from our website.
Increasing the number of IoCs could help improve protection
To help keep your network safe and protected, we identified several network artifacts that would be likely targets for attackers. This information was sourced from WHOIS data and DNS data.
The domains that are looked up for the purpose of domain name system (DNS) have been identified as search terms. These domains could connect to 49 IP addresses spread across 11 countries. The U.S tops the list, followed by the Netherlands in second place.

Unfortunately, IP addresses are still considered a low risk according to our latest malware check. We recommend monitoring for any signs of malicious activity as some of them were used as shared hosts for IoCs in the past.”
We looked closer at the WHOIS of the domains that we identified as IOCs and we found two email addresses (135224163[@]com & asdf921cn@com). They were used to register these domains.
“A research study that took place in 2016 showed that over 6000 domains could be related to each other. They were all found with different IP or email addresses. IT was also revealed by WHOIS records that most of those domains belong to…”
the domain name with the highest number to registrations was SnapNames LTD, which accounted for 10% of all domain names, among other companies shown in the figure.
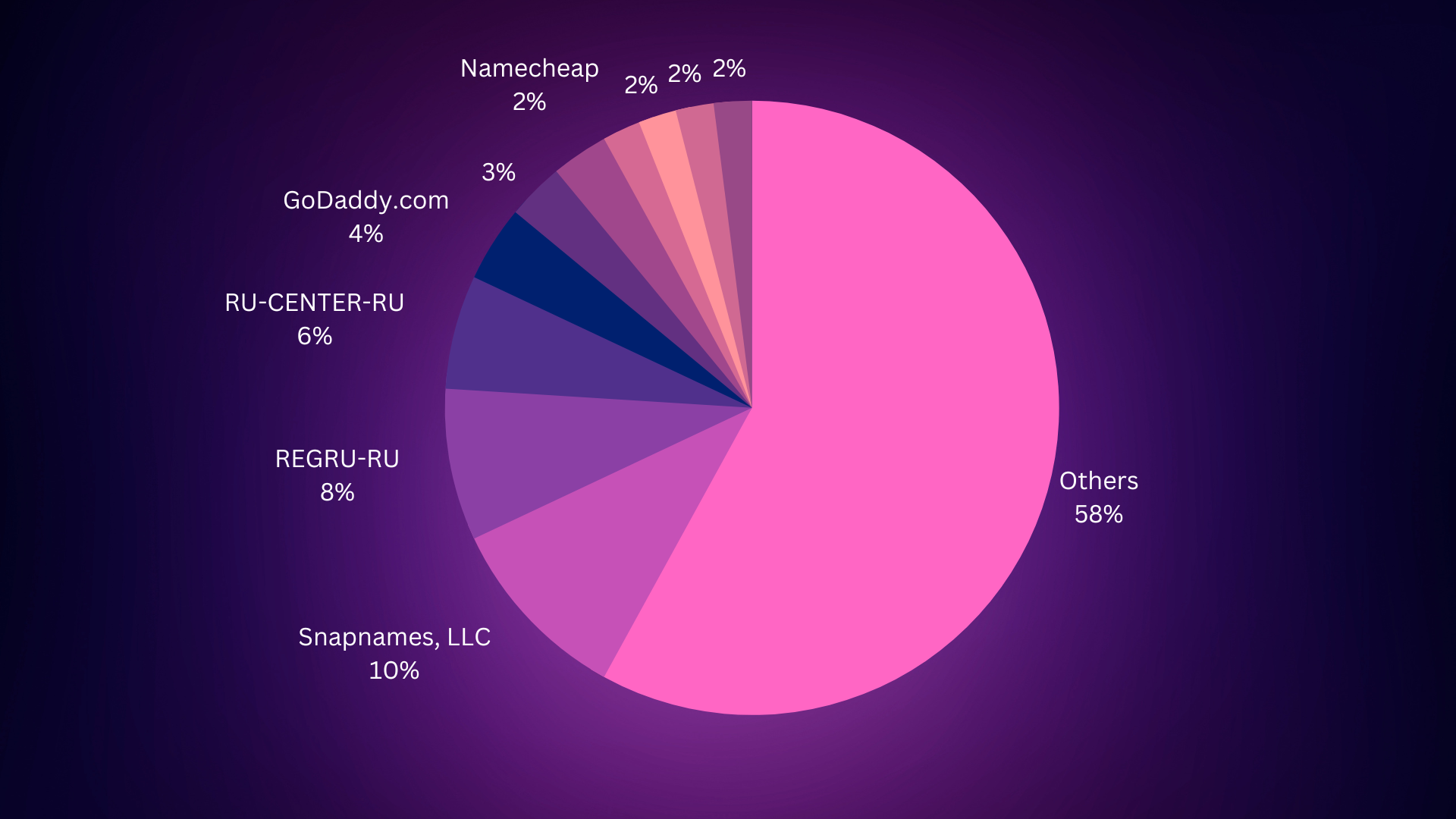
Though the chart’s data is not perfect, it does illustrate a general trend – most of IP addresses seem to be concentrated in one region and although the exact breakdown is not known, it appears that a lot of domains are registered by people from that same area too.
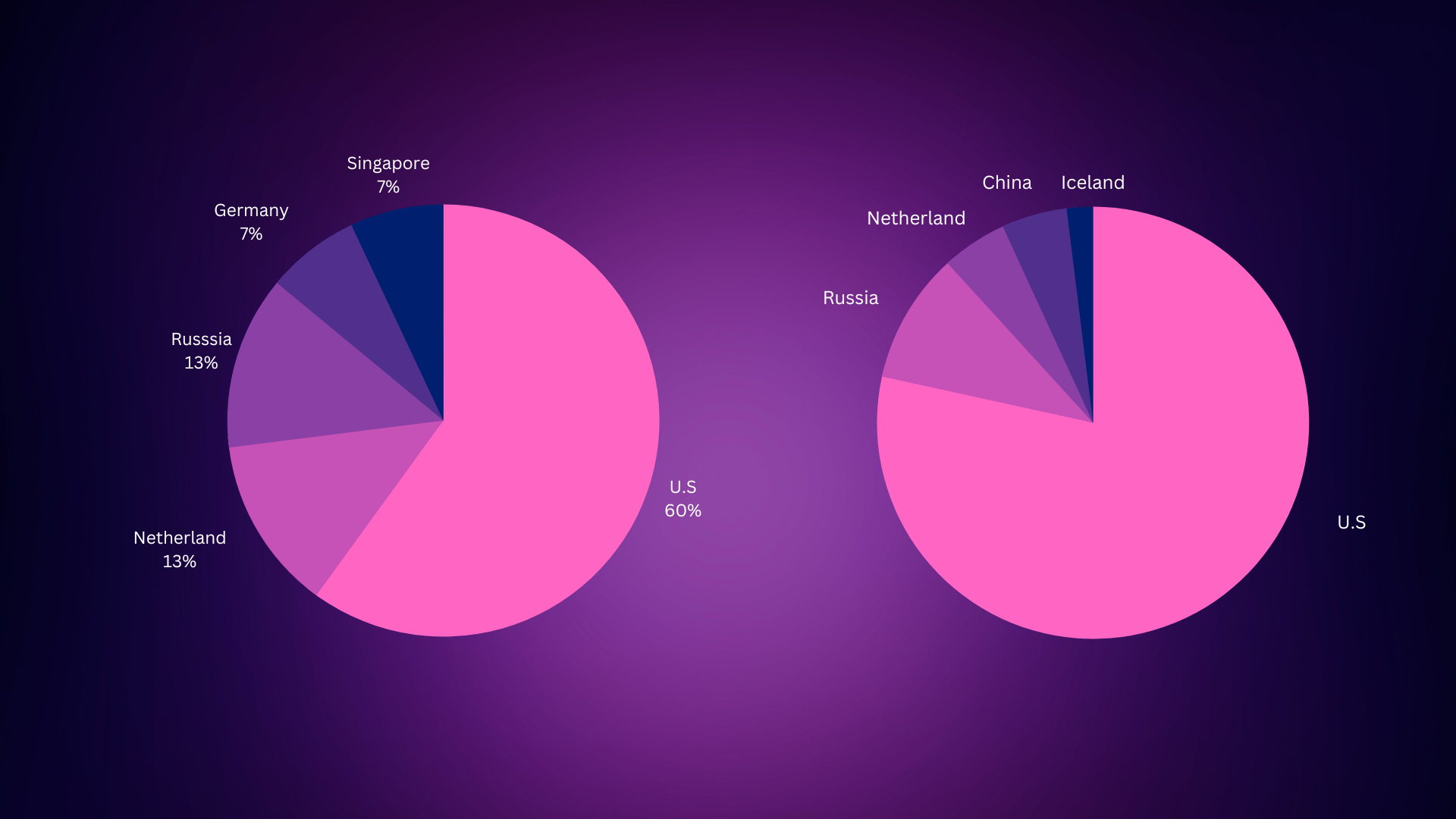
The United States, the Netherlands, and Russia consistently rank in either the top 5 countries for IP geolocation or domain registrations. That may not come as a surprise given that SnapNames, GoDaddy, NamePal, DropCatch, TurnCommerce and Namecheap are based in the U.S., while REGRU-RU, RU-CENTER-RU and Regional Network Information Center are based in Russia or RU.
As a final measure, we ran an automated check for malware over the 6,000+ domains that matched our criteria. We ended up finding 141 of these websites on various spam blacklists and known to be hosting malware.
BlackEnergy-Enabled Attack Prevention
Organizations that want to avoid the consequences that BlackEnergy poses, specifically an operational disruption, may want to block access to the domains identified as IoCs and any additional domains we found that may be connected. Another way to prevent hacking is to monitor connected IP addresses for any signs of suspicious activity.