Mantis is the most powerful botnet to date and is considered a serious threat. Mantis has a wide range of capabilities such as spamming, denial-of-service (DoS) attacks, mining cryptocurrencies and more. It is estimated that this botnet has generated $140 million in revenue for its operators.
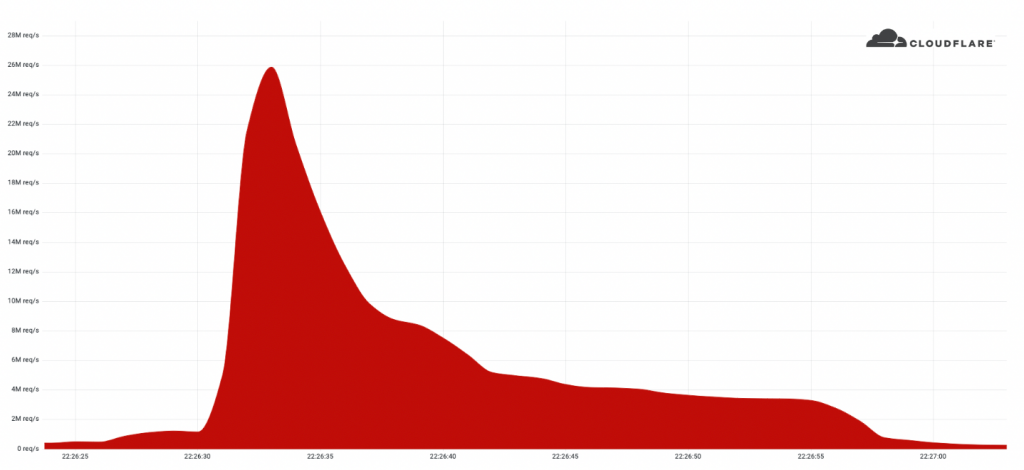
Last month in June, Cloudflare reported on the largest HTTPS DDoS attack that we’ve ever mitigated. At 26 million requests per second, it’s by far the biggest attack on record. Detected this attack and others, mitigating them before any significant damage was done. Since then, they have been keeping a close eye on this botnet called “Mantis” and where it directed its attacks against almost a thousand of Cloudflare customers.
Have you come across Mantis botnet before?
Mantis is a botnet that has been infecting computers since November 2017. It was found on the Internet by a security researcher, and then it was quickly identified as the source of a ransomware attack. Mantis is not just a ransomware. It can also be used to steal data, spy on users, and even mine cryptocurrency.
The Mantis botnet is based on an open-source program called “Miner-D” which mines for Monero (XMR). The miner-D program is also used in other malware like “Jaff” which mines for Bitcoin (BTC) and “LambdaLocker” which mines for Bitcoin Cash (BCH).
The StackBot is the first publicly disclosed and most likely the oldest known botnet that founds its niche in DDoSing targets. The name of the botnet that did 600Gbps DDoS attack was “Mantis”. As you can see, it’s not very powerful, but it also has potential just like Mantis shrimp. These small invertebrates measure less. The strength of the cephalopod’s claws will quickly break the surface tension of water and create a powerful shockwave that can travel fast through water at a recorded speed of 83 km/h. ##Similarly, the Mantis botnet uses approximately 5000 bots. Bots are capable of causing a significant strain on your cybersecurity and with them they can cause the most damaging attacks seen on the internet.
The mantis botnet is the latest creation of Windows malware with a rather simple goal: to send HTTP requests. Mantis can reach up to 26 million HTTPS requests per second, thanks to its 5000 bots. This means that on average, each bot sends 5200 HTTPS requests per second. 26M HTTP requests used to be hard. But thanks to Mantis, it’s possible to make the connection over HTTPS so that you won’t have any difficulty. A recent blog post highlighted the mathematics behind malware attack and how with HTTPS DDoS attacks, there is a higher cost involved because of the encryption used. Victims of HTTPS DDoS attacks can protect themselves by upgrading to TLS encryption.
Mantis is unlike traditional botnets, which generally consists of lots of internet-connected devices like DVRs, security cameras and smoke detectors. Mantis only relies on hijacked virtual machines and powerful servers These AI writers have access to powerful computational abilities, meaning that your business content won’t be spread too thin (and it will still be high quality).
Mantis is a follow-up to Meris, which was based originally on MikroTik devices. However, Mantis has now found its way into many more virtual machine platforms-ranging from Linux and Windows to VMWare and KVM- as well as running different applications such as HTTP proxies to run attacks. The name Mantis was chosen to be similar to “Meris” because it represents the origins of its programming. It’s also great for fast-paced growth since over the past few weeks, Mantis has been focused on 1,000+ Cloudflare customers.
What has Mantis been up to?
Cloudflare just released a new report by observations of the digital attack landscape. One important takeaway is that HTTP attacks are increasingly being used and they’ve grown by 72% in the past quarter. We’d like to think we’re contributing to that growth, but even so, an increasing digital threat is one never to be taken lightly. Over the past month, Mantis has used its botnet in over 3,000 traights to attack Cloudflare customers.
Mantis is a cyberthreat intelligence program with the goal of detecting cyber attacks. Mantis’ targets can be seen on their website, and the top industry being attacked is the Internet & Telecommunications industry, at 36% attack share. Second on the list was News Media & Publishing, followed by Gaming and Finance industries.
When you look at the location of the companies that were targeted, over 20% of them are US-based, 15% are Russia-based, and less than five percent are Turkey or France. This tells us how centralized attacks may be and how this number may be different if not for these attacks.
What are the ways to protect against a Mantis or other DDoS attacks?
Automated DDoS protection is a system that leverages dynamic fingerprinting to detect and mitigate DDoS attacks. Customers can get access to this system through the HTTP DDoS Managed Ruleset and enjoy protection against these types of attacks on their endpoints. The ruleset is enabled by default so there’s no need to take any action. Your computer is protected from this issue without changing any preferences or settings. If you’re concerned about DDoS, we also have tips for preventive measures and advice on how to respond. You can read the Best Practices: DoS records for even more tips and recommendations on how to optimize your Cloudflare.
It is now also possible to onboard HTTP applications that are not protected by Cloudflare using Magic Transit. These will be protected by L7 protection but it’s important to know that they won’t be accessible through http://[domain]. Spectrum customers can test WAF and CDN services in beta so they can carry HTTP traffic over the same IPs without risking latency