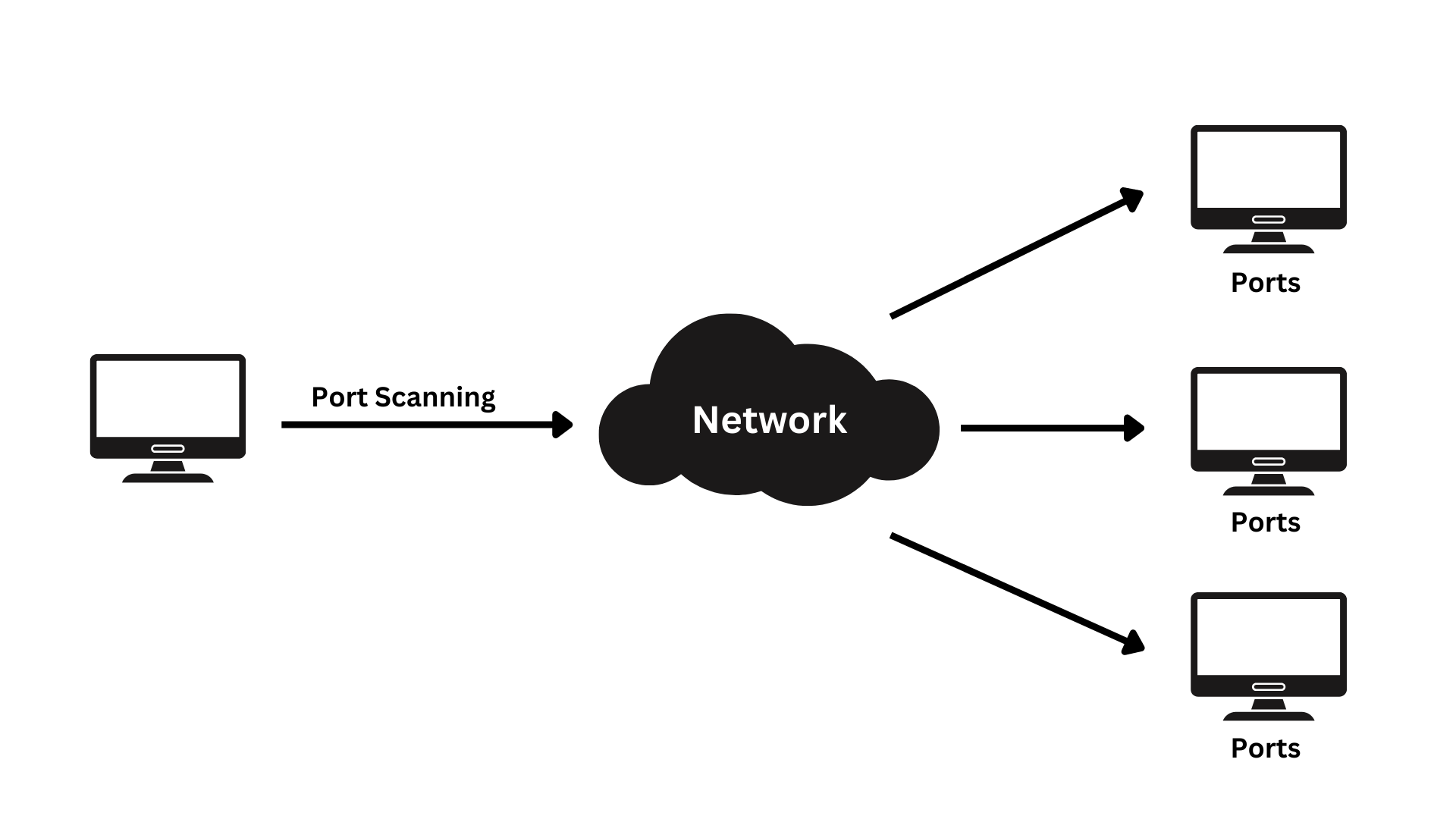
Port scanning is a process that enables you to find out what ports are open on a given IP address.
This process is usually done by sending connection requests to the port and checking for the response.
In some cases, the port will respond with an error message such as “connection refused” or “connection timed out.” In other cases, the port will respond with different information such as “port not found.”
Port scanning is a way of finding out which ports are open on a network. It involves sending packets and analyzing responses to find vulnerabilities.
This scanning can’t take place without first finding a list of active hosts on the network and then mapping those hosts to their IP addresses. Mapping starts with a network scan that identifies all the active machines on your network.
The goal of a port and network scan is to determine the organizational structure of IP addresses, hosts, and ports in order to create a map of your network. This should serve as a means for understanding where vulnerabilities that might put your servers at risk are located. It will also allow you to assess the security level at one glance. Network and port scanning can be used to test the network’s defences (like a firewall) which provides extra security against cyberthreats.
After a thorough network scan is complete and a list of active hosts is compiled, we can take a look for open ports that may enable unauthorized access by executing computer network port scans.
It’s important to note that scanning your network is used by both IT administrators and cybercriminals. One is usually the perpetrator of a cybersecurity breach, the other just wants to make sure everything’s being done safely. One of the most popular ways to attack a network is by performing a port scan. This includes host discovery, which, before an attack is carried out, acts as a guard of sorts reminding attackers that you’re aware they’re there. Network scanning is a crucial tool for network admins, so it’s important to monitor your network security levels. Network scans can indicate if there are any major security risks present on the network.
What are ports and port numbers?
Computer ports act as the gatekeeper for a program or Internet data and/or device-to-device communications. They are a central location where information can be exchanged electronically, whether on your own private network or through the Internet.
Port numbers are meant to maintain consistency and to coordinate programming. The port number combined with an IP address is what every internet service provider maintains in order to fulfill requests. The ports range from 0 to 65,536 and basically rank by popularity.
Ports 0 to 1023 are well known port numbers used for Internet access. You may have run into these before, although they can also have additional purposes like securing your router and other devices. These ports are governed by the Internet Assigned Numbers Authority (IANA). They’re held by some of the world’s most prestigious businesses, like Apple QuickTime, Microsoft MSN and so on. You might recognize some of these popular ports.
- Port 20 (UDP) holds FTP domain data transfer
- Port 22 (TCP) secure SSH protocol for secure logins, ftp and port forwarding.
- Port 53 (UDP) The Domain Name System is used to translate domain names into their corresponding IP address
- Port 80 (TCP) The World Wide Web is HTTP
Numbers 1024 through 49151 are considered “registered ports” or their number is reserved for software corporations. The numbers between 49,151 and 65,536 are dynamic ports that can be used by just about anyone
What are the protocols used in port scanning?
TCP and UDP are both internet data transmission protocols but transmit in different ways. TCP uses packets, of which the receiving end waits for an acknowledgement, whereas UDP is a datagram that does not need to be acknowledged.
TCP is a reliable connection-based two-way transmission of data that relies on the receiver’s status in order to be successful and complete. On the other hand, UDP is an unreliable, connectionless protocol. There may be times where data sent using UDP does not make it to its intended destination.
There are two protocols you can use to perform a port scan, and there are several different techniques that come with each one.
What are the different port scanning techniques?
There are a few different techniques for port scanning, but it all depends on what you’re looking for. Hackers will also use a specific technique if they’re trying to accomplish something in particular or according to their attack strategy.
Below are 3 of the most popular techniques, how they work and how to implement them.
- Ping scans: The simplest port scans are called ping scans, where a packet is sent to the target to verify that they are able to receive the data without errors. Ping scans are an automated way to sift through a range of IP addresses, by sending out internet control message protocol (ICMP) requests to different servers and waiting for responses. IT administrators may disable or troubleshoot the ping scan by using a firewall, thus making it impossible for attackers to find the network through pings.
- Half-open or SYN scans: A half-open scan is a way to check the status of a port without establishing the full connection. They can be used by attackers to detect whether or not a port is open. This port scan is sly. It starts the connection but doesn’t complete it, which means there would be no TCP handshake and the target device wouldn’t know that a connection was established.
- XMAS scans: With XMAS scans, you can be even less noticeable by firewalls. For instance, FIN packets are usually sent from server or client to terminate a connection after establishing a TCP 3-way handshake and successful transfer of data. You would find this in the message “there is no more data to be sent”. Firewalls typically focus on looking for SYN packets. Since FIN packets can’t be sent without a response, an XMAS scan is used to identify open ports by sending a packet with all flags set, including FIN and looking for the lack of response.
Port scanning results are differ by the type of scan.
After running a port scan, you can see what the network or server’s status is. There are three different categories: open, closed, and filtered.
- Open ports: An open port indicates that the target server or network is listening and responding to requests. It has sent a packet back saying it’s there. An open port can also be indicative of whether a service is being used and this is often the goal for cybercriminals when scanning ports. The success of a port scan could present itself as an avenue for an attack from cybercriminals. As an IT admin, it can be hard to maintain security while allowing access to necessary resources. Installing firewalls can help protect your company, but they may limit the connectivity of your users.
- Closed ports: Closed ports mean that the server or network received the request, but there is nothing “listening” on that port. A closed port is still accessible and could prove useful to IT administrators – it would quickly alert them if a host was on a specific IP address. They should still monitor closed ports in case they change to an open status, as this could create vulnerabilities. IT admins should consider using a firewall to block closed ports, which would then become “filtered” ports.
- Filtered ports: If no response is received, it could be that the host either didn’t hear the request (packet loss) or has a broken server. This usually means that the firewall did not let the packet through. If packets do not reach their target location, attackers can use this to get around security measures. It seems that many filtered ports are not able to connect or get an error message from the destination.
How can attackers use port scanning as an attack method?
According to the SANS Institute, one of the most popular ways to find a vulnerable server is with port scanning. They do this by scanning ports on other computers while looking for any that are open so they can attack them.
Cybercriminals often scan ports in order to see what security measures an organization has. They can then determine whether they want to target that company or not. A number of TCP protocol techniques actually make it possible for attackers to conceal their network location, use decoy traffic and perform port scans without being exposed.
Hackers want to find out more about you, so they’ll attack your machine and see what kind of reaction, or reaction this causes.
For example, a system will usually let you know if it’s been scanned. Hackers could then analyse the information and determine your operating system and security level.
Old and outdated, port scanning is no longer a reliable way to test for open ports. Protocols, tools and vulnerabilities are constantly evolving, so it’s important to make security changes around them. As a best practice approach, you should use logs and firewalls to monitor traffic to your ports, as this will help you identify any potential unauthorized entry points before an attacker can exploit them.

How can you prevent port scan attacks?
Port scanning is a popular method that cyber criminals use to find vulnerable servers. Most common TCP methods help attackers find potentially vulnerable networks and servers, hide the location of their attacked target, or both.
Cybercriminals search for and assess how you respond to their protocol attacks. They learn about your network to know the security and devices you use.
The threat landscape is constantly changing and it’s essential to have up-to-date threat intelligence in order to deal with port scan attacks. Businesses also need strong security software, port scanning tools, and security alerts that monitor ports and block malicious actors before they reach the network. Useful tools include IP scanning, Nmap, Netcat and more.
Other defense mechanisms include:
- Strong firewall: A firewall can prevent unauthorized access to your network. It identifies which ports are open and has the ability to shut down any port scan before it even starts.
- TCP wrappers: There are a number of ways in which this can be achieved. For example, administrators can create a whitelist (IP addresses and domain names that are allowed access) or blacklist (those who have been denied access).
- Uncover network holes: A port checker or port scanner can be used to identify if there are any ports open that you don’t need which could signify a potential security risk. Check them regularly to stay aware of potential vulnerabilities.




